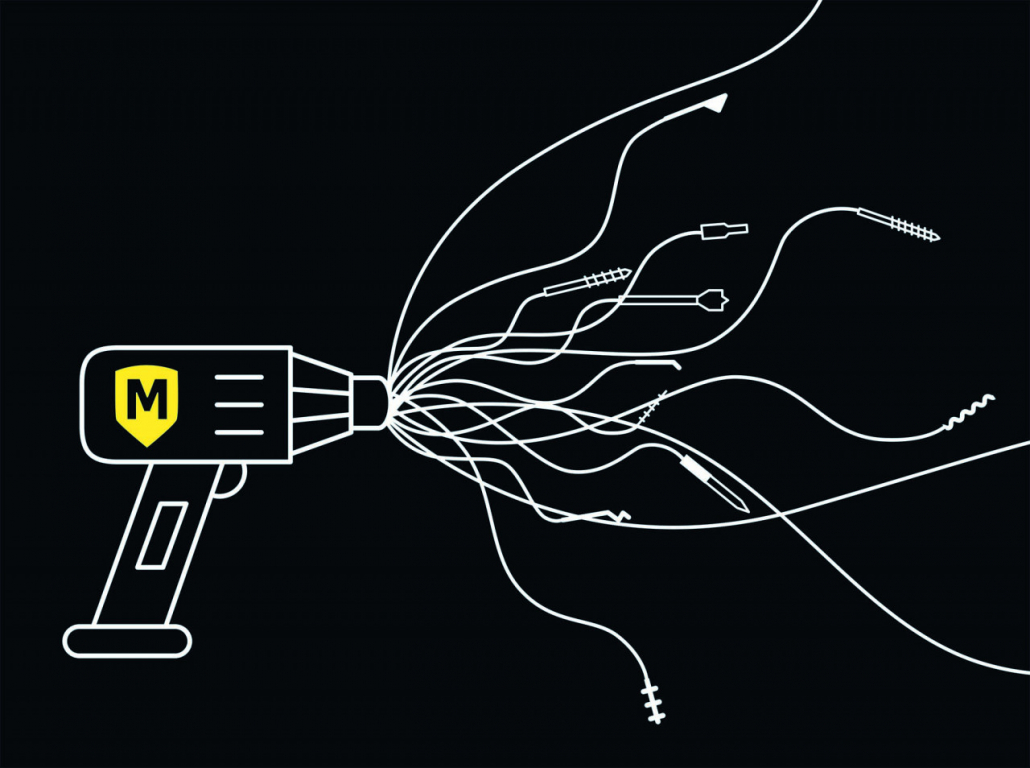
The Metasploit framework – what it does
It provides the ideal infrastructure to automate often tedious, mundane, and repetitive tasks. In the meantime, pen testers can concentrate on unique or specialized aspects of penetration testing and on identifying flaws within the security system.
Metasploit makes it easy to create one’s own tools for an attack. The EternalBlue exploit, which was mainly used for Wannacry attacks, was published by the Shadow Brokers in 2017 and packaged for Metasploit. This makes it a reliable tool for dealing with unpatched older Windows systems. Metasploit also has a large and constantly updated database of exploits in which a variety of different attack options can be searched to exploit the latest vulnerabilities.
Spy and attacker
Metasploit allows hackers to create a conducive environment to manipulate compromised machines, such as a Windows computer or server. It is an all-purpose tool to spy on targets, select one, choose the type of attack, create a payload and launch an attack. Almost every reconnaissance tool can be integrated with Metasploit. It is now common for zero-day reports to include a Metasploit module as proof of effectiveness.